Common WordPress attacks and how to protect yourself
Cybersecurity market is rapidly growing every day. More and more new specialists join the industry with more and more malware is being launched than ever before. According to Kaspersky Security, there are approximately 360K malware samples every day with 43% of cyber attacks target small business. Despite the enormous efforts that have gone into making sure WordPress is secure, there are still some aspects that are vulnerable to attacks. Let’s explore them.
Attack #1: Cross-site scripting (XSS)
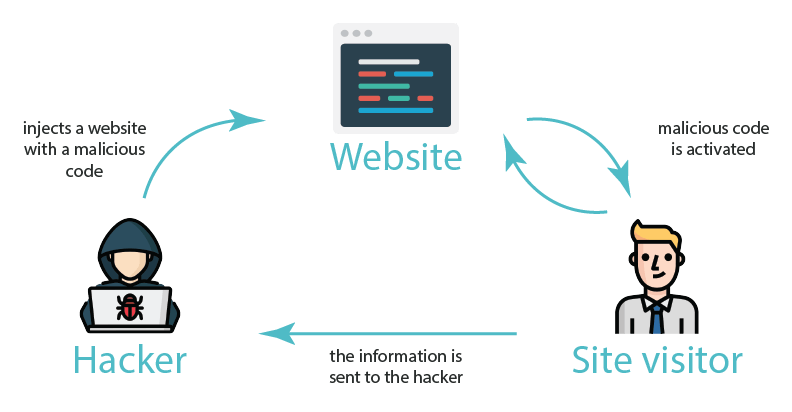 In 2013, a number of Yahoo accounts were hijacked. The hackers used cross-site scripting accounts. So, as you can see even big corporations are vulnerable to this type of attack. How it occurs? Briefly, it happens when JavaScript code is loaded via vulnerable dynamic site elements – such as contact forms and other user input fields. There are 3 of the most spread XSS forms:
In 2013, a number of Yahoo accounts were hijacked. The hackers used cross-site scripting accounts. So, as you can see even big corporations are vulnerable to this type of attack. How it occurs? Briefly, it happens when JavaScript code is loaded via vulnerable dynamic site elements – such as contact forms and other user input fields. There are 3 of the most spread XSS forms:
- Reflected XSS: includes unvalidated and unescaped user input as part of HTML output. Usually, people need to interact with malicious code in the link (for example, click on the ad)
- Stored XSS: the app needs to store user input that is viewed at a later time by another user
- DOM XSS: frameworks, app or API have already included attacker-controllable data.
How to defend?
To prevent this type of attacks, you need to simply escape your outputs correctly. The esc_url() function is a native WordPress function that replaces certain characters and defends your site from the XSS attacks.
Another way is to use wp_kses(), which filters the content and keeps only allowable HTML elements. $allowed_html = array( ‘a’ => array( ‘href’ => array(), ‘title’ => array() ), ‘br’ => array(), ’em’ => array(), ‘strong’ => array(), ); echo wp_kses( $custom_content, $allowed_html );
Attack #2: Brute Force
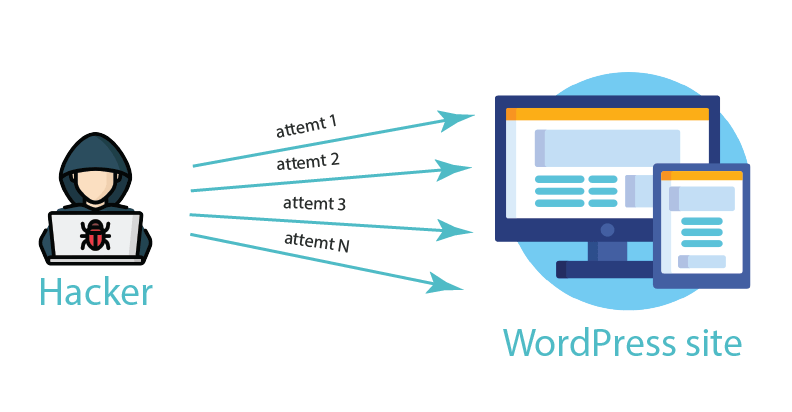 We are sure that you have already encountered situations where you do not remember the password or username and try to crack it. Brute force attack is about this. It involves multiple try and error approach using hundreds of combinations. By default, WordPress allows an unlimited number fail attempts, therefore the attacker can try thousands of combination per second. The utilize powerful algorithms and ready-to-use dictionaries.
We are sure that you have already encountered situations where you do not remember the password or username and try to crack it. Brute force attack is about this. It involves multiple try and error approach using hundreds of combinations. By default, WordPress allows an unlimited number fail attempts, therefore the attacker can try thousands of combination per second. The utilize powerful algorithms and ready-to-use dictionaries.
How to defend?
First up, do not use a standard username and password. The vast majority of hackers assume people are using the username ‘admin’. It is because in early WordPress versions ‘admin’ was by default. In order to create a solid password, use different online password generators:
- Passwords Generator
- Last Pass
- Random.org
- RoboForm.
Attack #3: SQL Injection
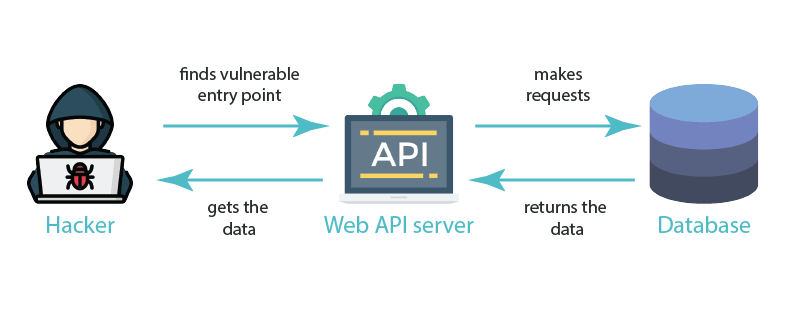 It is one of the most popular types of attack. A lot of major companies and organizations have already struggled from this. As an example, NASA (2009) or Barracuda (2011). SQL Injections is something similar to XSS, because it needs a vulnerable entry point, but it directly affects your database. WordPress as any other platform relies on the database layer, where users store their information. For example, if you are running an e-commerce store, your database will contain the information about orders, customers, and site configuring data.
It is one of the most popular types of attack. A lot of major companies and organizations have already struggled from this. As an example, NASA (2009) or Barracuda (2011). SQL Injections is something similar to XSS, because it needs a vulnerable entry point, but it directly affects your database. WordPress as any other platform relies on the database layer, where users store their information. For example, if you are running an e-commerce store, your database will contain the information about orders, customers, and site configuring data.
How to defend?
To complete an SQL Injection attack, hackers use a request parameter through an input field or an URL. There they run a customized database command. There are different ways to protect your database. Firstly, make sure that you have changed its prefix from “wp_” on another one. There is a great article, that is explained how to do this. Then, explore the WordPress API functions. Some of them were created especially to help protect inputted data from SQL injections. As an example, add_post_meta(). It adds a metadata field to a post, meaning you can use an INSERT INTO command in a secure way, cause you don’t have to add database calls manually to your code. Also, do not forget to back up your site. It is not related to SQL Injection but will help to recover your site in case of hacking and stealing information.
- DropBox
- Amazon S3
- Google Drive back-up
- FTP
- Email.
![]()
![]() Attention!
Attention!
You should always update the WordPress site and use only reliable plugins
![]() So, now you are familiar with the most popular types of attacks occurred on WordPress. Of course, even if you ensure yourself with the tools to prevent these attacks, it is not 100% guaranteed that you are not vulnerable. The last piece of advice is to always update the WordPress site and use only reliable plugins. Check out this WordPress comparison table plugin for an easy way to display and manage information on your WordPress site
So, now you are familiar with the most popular types of attacks occurred on WordPress. Of course, even if you ensure yourself with the tools to prevent these attacks, it is not 100% guaranteed that you are not vulnerable. The last piece of advice is to always update the WordPress site and use only reliable plugins. Check out this WordPress comparison table plugin for an easy way to display and manage information on your WordPress site